The General Data Protection Regulation (GDPR) is a regulation in EU law on data protection and privacy in the European Union (EU) and the European Economic Area (EEA) that was put into effect on May 25th, 2018, as part of the European Union’s protection reform. It aims to protect the personal data and privacy of all the people who are part of the European Union.
It’s the strictest protection and privacy law in the world, and penalties for non-compliance are severe from a legal and business perspective. Yet, few organizations are 100% compliant with its regulations. That’s why you’ll learn all about how to implement GDPR compliance for your organization and additional information about removing mailboxes and Axigen’s privacy policy.
* Axigen customers can visit their account managers for more information, but please note, not everyone reading this is a current Axigen customer.

Areas that Need to Be Addressed for GDPR Compliance
GDPR applies to you regardless of your or your enterprise’s location if:
- you are a company, government agency, non-profit, or another organization that offers goods and services to people in the European Union (EU),
- It’s important to note here that all online businesses must be GDPR compliant at the very least as a protective measure, as you may transact with people in the EU (and not be aware of it).
- you collect and analyze data for EU residents.
The difference between Data Controllers and Processors:
- Data controllers are defined as any individual, agency, public authority, or another body that determines the means and purpose of processing personal data. Controllers decide how personal data gets processed.
- Processors are defined as any individual, agency, public authority, or another body that processes personal data on behalf of a controller. Processors don’t make decisions about how personal data gets processed. However, they must still be GDPR compliant because they handle personal data.
Art. 4 GDPR states that personal data is any data linked to the identity of a living person. This includes financial information, addresses, and indirect links, such as evaluations relating to a person’s behavioral patterns. Personal data can also include video, audio, images, words, and numerals.
There is a GDPR checklist for data controllers available that ensures you secure your organization, protect your customer’s data, and avoid fines for non-compliance in the following areas:
- Lawful basis and transparency
- Data security
- Accountability and governance
- Privacy rights
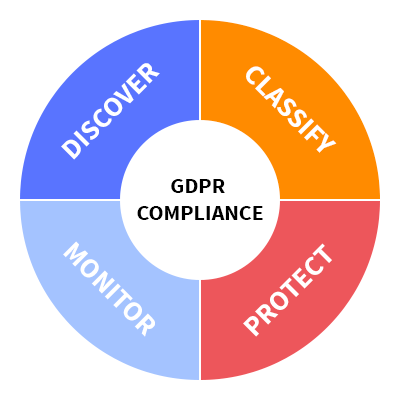
Additionally, consider the following areas for GDPR compliance for on-premises data:
- Discover
- Classify
- Protect
- Monitor
Securing GDPR Compliance for Your Organization
Compliance with GDPR doesn’t simply mean following its requirements. It means that there is careful consideration of all points of client interaction with policies and procedures in place. Ensure that you review these policies and procedures regularly to secure ongoing compliance.
Step 1: Legal Research & Benchmarking
The first couple of steps you must take to secure GDPR compliance are to:
- understand your GDPR requirements and
- engage with your legal and compliance teams.
Start by benchmarking your readiness and get recommendations for any next steps. Continue to work with your legal and compliance teams and other key internal and external stakeholders to establish guidelines for responding to Data Subject Requests (DSARs). Your organization should also perform a GDPR compliance gap analysis and establish a roadmap to compliance.
Data Subject Requests
Data subject = an identified or identifiable natural person; someone who can be identified by reference to an identifier, either directly or indirectly. Identifiers include:
- a name
- an identification number
- location data
- an online identifier or to one or more factors specific to the identity of that natural person, including physiological, physical, mental, genetic, economic, social, or cultural.
Recital 1 of the GDPR (“data protection as a fundamental right”) states that everyone has the fundamental right to the protection of the processing of their personal data, which encompasses anything from art. 13, 14, 15 to 22, including art. 34.
Data subject requests = “the right to find out whether or not personal data concerning him or her are being processed” — Article 15.
A data subject must send a request to the data controller to exercise any of their consumer rights from the above articles. According to Article 12, the controller must then “take appropriate measures” to provide any information relating to the processing of data for the data subject.
You can find more information about DSARs and how to respond to them here.
Step 2: Internal Data Audit
Continue by discovering the types of personal data you are storing and where it resides to comply with DSARs.
IT security and privacy continue to be major tech challenges that organizations face today due to the growing digital transformation efforts and the constant changes in the regulatory environment. There’s added pressure for organizations to get privacy and security right — particularly so if they are large and have a reputation.
Take the following things into consideration before an audit occurs:
- IT model – Is your organization using appropriate controls, regardless of where it processes and stores information (on-premises or with a hosted cloud provider)?
- Workflows – How is information transmitted internally and externally? Who has access to it, and how is highly sensitive information classified?
- Social media – Are there policies in place, and are they followed to avoid accidental disclosure of sensitive information directly or through correlating and aggregating data sources?
- Wireless / mobile technology – Is there a policy for personal devices, and does it address aspects such as unique hardware identifiers, location identifiers, or non-secure off-premises Wi-Fi connections?
Additionally, the privacy and security controls that organizations use may include:
- Data encryption, both in transit and at rest
- Privacy and access controls for databases, such as partitioning
- Privileged user management, including restricted access to sensitive information based on user role and job function
- Multi-factor authentication
- Privacy policies that are documented, reviewed regularly, and communicated to vendors, employees, and other stakeholders
- Ongoing training programs for staff on best practices, and privacy and security threats.
Step 3: Implement Compliance Requirements & Assist Users
Next, start implementing compliance requirements using appropriate data governance and compliance capabilities. Assist users in identifying and classifying personal data, as defined by the GDPR.
GDPR is complex in the sense that some of the requirements are vague, leaving much to interpretation. Therefore, compliance depends on the nature of personal data and the volume of information that’s processed. Additionally, the organizations’ size doesn’t matter; instead, the requirements are based on the scale of data processing.
Consider seeking a third-party expert’s services or appointing an in-house data protection officer to ensure GDPR compliance and acquire specialized knowledge to further understand data processing requirements.
Axigen Product Security Capabilities Safeguard against GDPR Breaches
Use Axigen’s product security capabilities to prevent data leaks and breaches and implement protections for personal data in the following areas:
- Protect end-user and administrator accounts
- Implement data breach prevention and response and protect against malicious code
- Use audit logging to monitor for potentially malicious activity and enable forensic analysis of data breaches
- Consider implementing simple manual policies to identify and protect sensitive data
- Prevent the most common attack vectors, including phishing emails and documents containing malicious links and attachments by activating Premium AntiVirus and AntiSpam layers.
Further activities and implementations might be required on a case-by-case basis.
Identifying In-scope Content
Axigen uses two primary storage repositories for end user-generated content:
- mailboxes
- public folders.
Content stored in an individual user's mailbox
Each mailbox is uniquely associated with the specific user and represents their default repository within Axigen. The stored data in a user mailbox includes content created using WebMail, Outlook, Thunderbird, or any other end-user email client application tools (that connect to Axigen’s servers using POP, IMAP, SMTP, and others) as well as incoming email messages from other users from the same organization as well as external users.
Examples of data beyond email messages include calendar items (meetings and appointments), contacts, tasks, and notes. Deleting an individual user's mailbox removes content generated by or sent directly to the user in the context of their mailbox. You can delete user mailboxes by using the Axigen WebAdmin or CLI interfaces.
Content stored in public folders
Public folders are shared storage implementations that aren’t associated with a specific user. Instead, users have access to shared (public) folders to generate content. Client tools (for example, Axigen WebMail and IMAP Client apps) are the primary mechanism for managing content in public folders. The Axigen WebAdmin interface provides facilities for managing public folder objects but not individual content items within the public folder.
The primary requirement will be managing individual user mailbox content (this requirement can be easily addressed through WebAdmin or CLI tools that you regularly use to manage mailboxes). If you must process content across multiple mailboxes or types of resources, WebMail access using the postmaster account is the preferred mechanism within Axigen to identify in-scope content.
Removing Mailboxes
When an Axigen mailbox gets deleted, it will permanently remove (purge) all data associated with that mailbox. You can do that here, including finding how to edit an existing account or create a new one.
Automatic Data Collection Reported to Axigen by the Axigen Server Software
The Axigen Privacy policy states how we collect and use personal data about our customers, in accordance with GDPR and other national implementing laws, regulations, and secondary legislature, when accessing the website or using the Software Product. We do not provide, sell, or make this information available, except in the case of a lawful intercept request.
Check back frequently for any changes to the privacy policy, as it can change without notice.
Additional resources to check out:
- How email archiving helps you access and backup your data
- A comprehensive guide to securing your mail server
- How To Increase Brute-Force Attack Protection Using Axigen’s Fail2Ban Linux Integration
- How to increase email security with Axigen.
Safeguard GDPR Compliance with a Mail Server Made in Europe
When collecting data, you must understand where this data is stored and how to easily move it. If a user asks for their data under GDPR, you must have the proper policies and procedures in place to comply, which can become difficult without the right solutions.
Thankfully, Axigen is a European business, therefore, it is fully GDPR compliant and experienced in dealing with requirements. Remember, there is no completely secure system anywhere in the world. However, a highly secure email server with comprehensive packages covering security from all layers is possible with Axigen.