This article describes how you can synchronize your Axigen server with an LDAP, specifically an Axigen to LDAP synchronization.
Solution
Starting with Axigen 7.0, administrators have the option to synchronize the Axigen server domain information with a LDAP database. The supported options are:
2-Way synchronization
Axigen to LDAP synchronization
LDAP to Axigen synchronization
The synchronization will occur for:
- Axigen 7.0 version or later
- OpenLDAP 2.4.x version or later
- the following overlays must be active in the OpenLDAP installation:
* syncprov
* memberof
These overlays should be present in the standard OpenLDAP distribution
modules path as files suffixed with ".la".
WARNING: Please back up the existing LDAP installation before implementing the Axigen <-> LDAP synchronization. This step is very important because the Axigen to LDAP synchronization can lead to modifications of your LDAP database and as such you could find the respective database will not be usable in other integrations you might have previously configured.
OpenLDAP configuration
After meeting the above requirements you must download the Axigen OpenLDAP Schema from the corresponding download section on our website:
https://www.axigen.com/mail-server/download-axigen-openldap-schema.html
The above archive contains a schema file named axigen.schema. Place this file in the standard schema location for your LDAP server, usually /etc/openldap/schema/ or /etc/ldap/schema/.
Now you must make the following modifications to the OpenLDAP server configuration file slapd.conf.
1) The axigen.schema file must be included along with the other required
schemas. To accomplish this add the following line to the required configuration file section.
Example:
include /etc/openldap/schema/axigen.schema
2) Each OpenLDAP server used must be configured with a unique identifier, by using the 'serverID' directive.
Example:
serverID 1
3) The "modulepath" attribute, if not specified, must point to the directory
where all modules reside:
Example:
modulepath /usr/lib/openldap
4) Then, the required modules must be specified to be loaded at startup:
Example:
moduleload syncprov.la
moduleload memberof.la
5) The two modules specified above must be configured within your LDAP database specification section as per the following sample:
Example:
# Replication support enabled (for cookies)
overlay syncprov
syncprov-checkpoint 100 30
syncprov-sessionlog 100
# Member-of support enabled
overlay memberof
memberof-refint true
6) As definition for indexing attributes, you should consider adding entries for attributes such as entryCSN
Example:
# Indexing options for database
index entryUUID,entryCSN eq
7) For our example we will consider the following rootdn/rootpw definitions
Example:
rootdn "cn=admin,dc=example,dc=test"
rootpw pa$$w0rd
8) Restart the ldap service.
An example of the minimum requirements for the spald.conf is:
After making the above configuration changes to your LDAP server, you should populate the directory with information on the different organizations, organizationalUnits and remainder of objects that need to exist here.
Below you can find an example LDIF for an imaginary organization and two branches (Users/Groups) used for the synchronization with the internal Axigen database.
Place the above entries in a .ldif file, modifying the domain name example.test to match your own, and then you can use the following command to add it to the LDAP database:
ldapadd -D "cn=admin,dc=example,dc=test" -W -x -f filename.ldif
You will be asked for the password you set up in the /etc/openldap/slapd.conf
An output similar to this will be returned:
To check that the above entries were added use:
ldapsearch -b "dc=example,dc=test" -D "cn=admin,dc=example,dc=test" -W -x
Axigen Mail Server configuration
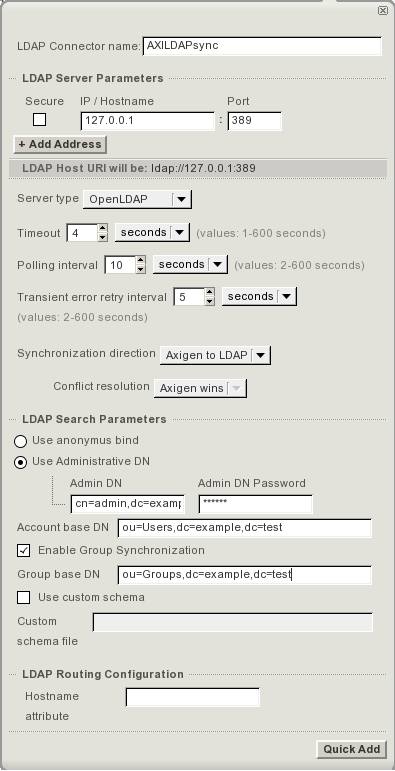
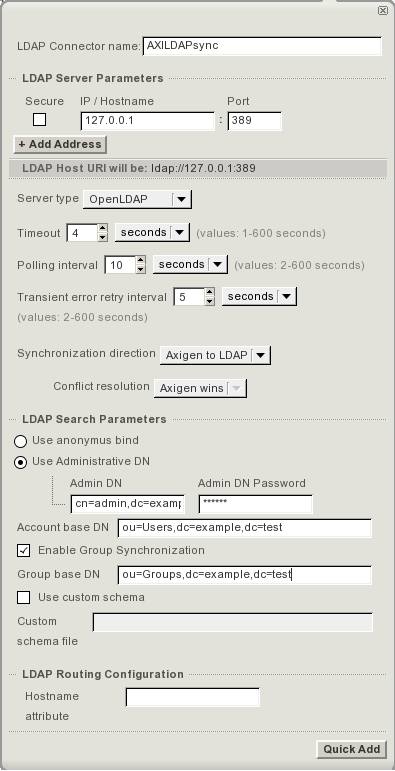
1) Create a new LDAP Connector.
- Go to Webadmin -> Clustering -> Clustering Setup -> LDAP Connectors tab -> Connector List section -> press the "Add Connector" button.
In the "LDAP Server Parameters" enter:
- the IP/Hostname and Port on wich the LDAP server is listening.
- from the "Server type" drop-down box make sure you select
"OpenLDAP"
- in this section you can also set the "Timeout", "Polling interval" and "Transient error retry interval" parameters, that relate to the timing details for the Axigen -> LDAP communication.
- select the required synchronization method from the drop-down box related to the "" entry. For the configuration presented in this article choose "Axigen to LDAP".
For the "LDAP Search Parameters" use:
- choose the "Use Administrative DN" - This option instructs Axigen to authenticate, using the defined user, to the LDAP server before requesting information. This user is the admin user defined in the LDAP rootdn configuration.
- enter the proper "Admin DN" and "Admin DN Password". In our case these are:
Admin DN:
Admin DN Passord:
- in the "Account base DN" field enter:
- check the box related to the "Enable Group Synchronization" option and enter for the "Group base DN" field:
- click the "Quick Add" button at the bottom of the wizard page.
Below you can find a screenshot detailing the required configuration parameters:
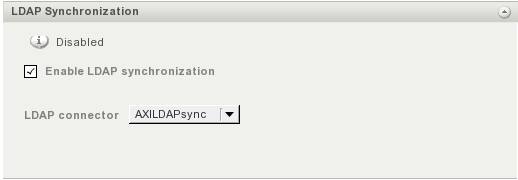
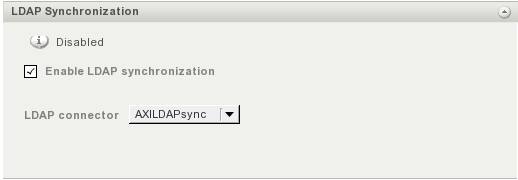
2) Enable LDAP synchronization for the required domain via Webadmin -> Domains & Accounts -> Manage Domains -> click the "Edit" button corresponding to the desired domain -> General tab -> LDAP Synchronization section -> check the box related to the "Enable LDAP synchronization" option and choose from the below drop-down box the LDAP connector you have specifically set-up and click the "Save Configuration" button at the bottom of the page.
To test the above configured Axigen to LDAP synchronization create a new account in your domain via Webadmin. After this check to see if it was automatically added in the LDAP database.
NOTE: In our case of Axigen to LDAP synchronization, accounts that already exist in the respective domain, before making the above Axigen configurations, will be added and synced with the LDAP database, when their parameters are first modified.
The synchronization will occur for:
- Account/Group creation/deletion
- Account configuration
- Group membership
- Axigen 7.0 version or later
- OpenLDAP 2.4.x version or later
- the following overlays must be active in the OpenLDAP installation:
* syncprov
* memberof
These overlays should be present in the standard OpenLDAP distribution
modules path as files suffixed with ".la".
WARNING: Please back up the existing LDAP installation before implementing the Axigen <-> LDAP synchronization. This step is very important because the Axigen to LDAP synchronization can lead to modifications of your LDAP database and as such you could find the respective database will not be usable in other integrations you might have previously configured.
OpenLDAP configuration
After meeting the above requirements you must download the Axigen OpenLDAP Schema from the corresponding download section on our website:
https://www.axigen.com/mail-server/download-axigen-openldap-schema.html
The above archive contains a schema file named axigen.schema. Place this file in the standard schema location for your LDAP server, usually /etc/openldap/schema/ or /etc/ldap/schema/.
Now you must make the following modifications to the OpenLDAP server configuration file slapd.conf.
1) The axigen.schema file must be included along with the other required
schemas. To accomplish this add the following line to the required configuration file section.
Example:
include /etc/openldap/schema/axigen.schema
2) Each OpenLDAP server used must be configured with a unique identifier, by using the 'serverID' directive.
Example:
serverID 1
3) The "modulepath" attribute, if not specified, must point to the directory
where all modules reside:
Example:
modulepath /usr/lib/openldap
4) Then, the required modules must be specified to be loaded at startup:
Example:
moduleload syncprov.la
moduleload memberof.la
5) The two modules specified above must be configured within your LDAP database specification section as per the following sample:
Example:
# Replication support enabled (for cookies)
overlay syncprov
syncprov-checkpoint 100 30
syncprov-sessionlog 100
# Member-of support enabled
overlay memberof
memberof-refint true
6) As definition for indexing attributes, you should consider adding entries for attributes such as entryCSN
Example:
# Indexing options for database
index entryUUID,entryCSN eq
7) For our example we will consider the following rootdn/rootpw definitions
Example:
rootdn "cn=admin,dc=example,dc=test"
rootpw pa$$w0rd
8) Restart the ldap service.
An example of the minimum requirements for the spald.conf is:
slapd.conf
=======
include /etc/openldap/schema/core.schema
include /etc/openldap/schema/cosine.schema
include /etc/openldap/schema/inetorgperson.schema
include /etc/openldap/schema/misc.schema
include /etc/openldap/schema/axigen.schema
pidfile /var/run/openldap/slapd.pid
argsfile /var/run/openldap/slapd.args
serverID 1
database bdb
suffix "dc=example,dc=test"
rootdn "cn=admin,dc=example,dc=test"
rootpw pa$w0rd
directory /var/lib/openldap-data
index objectClass eq
index ou,cn,mail,surname,givenname eq,pres,sub
index entryUUID,entryCSN eq
moduleload memberof.la
moduleload syncprov.la
overlay syncprov
syncprov-checkpoint 100 30
syncprov-sessionlog 100
overlay memberof
memberof-refint true
After making the above configuration changes to your LDAP server, you should populate the directory with information on the different organizations, organizationalUnits and remainder of objects that need to exist here.
Below you can find an example LDIF for an imaginary organization and two branches (Users/Groups) used for the synchronization with the internal Axigen database.
# example.test
dn: dc=example,dc=test
objectClass: dcObject
objectClass: organization
dc: example
o: test
# Users, example.test
dn: ou=Users,dc=example,dc=test
objectClass: organizationalUnit
ou: Users
# Groups, example.test
dn: ou=Groups,dc=example,dc=test
objectClass: organizationalUnit
ou: Groups
Place the above entries in a .ldif file, modifying the domain name example.test to match your own, and then you can use the following command to add it to the LDAP database:
ldapadd -D "cn=admin,dc=example,dc=test" -W -x -f filename.ldif
You will be asked for the password you set up in the /etc/openldap/slapd.conf
An output similar to this will be returned:
adding new entry "dc=example,dc=test"
adding new entry "ou=Users,dc=example,dc=test"
adding new entry "ou=Groups,dc=example,dc=test"
To check that the above entries were added use:
ldapsearch -b "dc=example,dc=test" -D "cn=admin,dc=example,dc=test" -W -x
Axigen Mail Server configuration
1) Create a new LDAP Connector.
- Go to Webadmin -> Clustering -> Clustering Setup -> LDAP Connectors tab -> Connector List section -> press the "Add Connector" button.
The connector options should be entered based on the settings of your LDAP server. Enter a name for the connector in the "LDAP Connector name" field.
In the "LDAP Server Parameters" enter:
- the IP/Hostname and Port on wich the LDAP server is listening.
- from the "Server type" drop-down box make sure you select
"OpenLDAP"
- in this section you can also set the "Timeout", "Polling interval" and "Transient error retry interval" parameters, that relate to the timing details for the Axigen -> LDAP communication.
- select the required synchronization method from the drop-down box related to the "" entry. For the configuration presented in this article choose "Axigen to LDAP".
For the "LDAP Search Parameters" use:
- choose the "Use Administrative DN" - This option instructs Axigen to authenticate, using the defined user, to the LDAP server before requesting information. This user is the admin user defined in the LDAP rootdn configuration.
- enter the proper "Admin DN" and "Admin DN Password". In our case these are:
Admin DN:
cn=admin,dc=example,dc=test
Admin DN Passord:
pa$w0rd
- in the "Account base DN" field enter:
ou=Users,dc=example,dc=test
- check the box related to the "Enable Group Synchronization" option and enter for the "Group base DN" field:
ou=Groups,dc=example,dc=test
- click the "Quick Add" button at the bottom of the wizard page.
Below you can find a screenshot detailing the required configuration parameters:
2) Enable LDAP synchronization for the required domain via Webadmin -> Domains & Accounts -> Manage Domains -> click the "Edit" button corresponding to the desired domain -> General tab -> LDAP Synchronization section -> check the box related to the "Enable LDAP synchronization" option and choose from the below drop-down box the LDAP connector you have specifically set-up and click the "Save Configuration" button at the bottom of the page.
To test the above configured Axigen to LDAP synchronization create a new account in your domain via Webadmin. After this check to see if it was automatically added in the LDAP database.
NOTE: In our case of Axigen to LDAP synchronization, accounts that already exist in the respective domain, before making the above Axigen configurations, will be added and synced with the LDAP database, when their parameters are first modified.
OS:
LinuxWindowsFreeBSDNetBSDOpenBSDSolaris
Distros:
WindowsDEB based distros amd64FreeBSD 7.x