Updated: December 5, 2024
At Axigen, we’re committed to ensuring 100% security of your mail server and the highest rate of email deliverability.
This is why, starting with Axigen X3 Update 2, we’re rolling out Milter V6 Support which allows the integration of the Axigen Mail Server with OpenDMARC and RSPAMD.
As you probably already know, the DMARC protocol is designed with email domain owners in mind, giving them the ability to protect their domain from unauthorized use, or what is more commonly known as email spoofing.
In this article, we’ll show you a step-by-step tutorial on how to integrate openDMARC via Milter with the latest update of Axigen X3.
You’ll see how to install on CentOS 7, from configuration and service setup, to the actual Axigen integration. We’ll also show you what logging looks like, how to check test results, complete with header examples, how to filter messages based on DMARC policy.
Here’s what you need to know.

What Is DMARC?
DMARC, which stands for “Domain-based Message Authentication, Reporting & Conformance”, is an email authentication, policy, and reporting protocol. It builds on the widely deployed SPF and DKIM protocols, adding linkage to the author (“From:”) domain name, published policies for recipient handling of authentication failures, and reporting from receivers to senders, to improve and monitor protection of the domain from fraudulent email.
By implementing DMARC, you protect a domain from being used in business email compromise attacks, phishing emails, email scams and other cyber threat activities.
How Does DMARC Work?
To pass DMARC, a message must pass SPF authentication and SPF alignment and/or DKIM authentication and DKIM alignment. If the message fails both (1) SPF or SPF alignment and (2) DKIM or DKIM alignment, that means the message will also fail the DMARC protocol.
You can find more information about configuring DNS settings here, which is especially useful if you’re trying to configure an email server in production.
What Is openDMARC?
OpenDMARC, on the other hand, is an open source implementation of the Domain-based Message Authentication, Reporting and Conformance specification.
If you’re looking for even more information on the topic, you can check out this RFC from IETF Tools, this GitHub thread on DMARC open source implementation, as well as the openDMARC manual.
How to Integrate Axigen X3 with openDMARC via Milter V6
Step 1: Install openDMARC on CentOS 7 (via Epel)
...
Dependencies Resolved
=============================================================================================================================================================================================================================================
Package Arch Version Repository Size
=============================================================================================================================================================================================================================================
Installing:
opendmarc x86_64 1.3.2-1.el7 epel 94 k
Installing for dependencies:
libopendmarc x86_64 1.3.2-1.el7 epel 30 k
libspf2 x86_64 1.2.10-5.20150405gitd57d79fd.el7 epel 66 k
mailcap noarch 2.1.41-2.el7 base 31 k
perl-Business-ISBN noarch 2.06-2.el7 base 25 k
perl-Business-ISBN-Data noarch 20120719.001-2.el7 base 24 k
perl-Compress-Raw-Bzip2 x86_64 2.061-3.el7 base 32 k
perl-Compress-Raw-Zlib x86_64 1:2.061-4.el7 base 57 k
perl-DBD-MySQL x86_64 4.023-6.el7 base 140 k
perl-DBI x86_64 1.627-4.el7 base 802 k
perl-Data-Dumper x86_64 2.145-3.el7 base 47 k
perl-Encode-Locale noarch 1.03-5.el7 base 16 k
perl-HTTP-Date noarch 6.02-8.el7 base 14 k
perl-HTTP-Message noarch 6.06-6.el7 base 82 k
perl-IO-Compress noarch 2.061-2.el7 base 260 k
perl-IO-HTML noarch 1.00-2.el7 base 23 k
perl-LWP-MediaTypes noarch 6.02-2.el7 base 24 k
perl-Net-Daemon noarch 0.48-5.el7 base 51 k
perl-PlRPC noarch 0.2020-14.el7 base 36 k
perl-Switch noarch 2.16-7.el7 base 22 k
perl-TimeDate noarch 1:2.30-2.el7 base 52 k
perl-URI noarch 1.60-9.el7 base 106 k
Transaction Summary
=============================================================================================================================================================================================================================================
Install 1 Package (+21 Dependent packages)
Total download size: 2.0 M
Installed size: 4.7 M
Is this ok [y/d/N]: y
Downloading packages:
(1/22): libopendmarc-1.3.2-1.el7.x86_64.rpm | 30 kB 00:00:00
(2/22): libspf2-1.2.10-5.20150405gitd57d79fd.el7.x86_64.rpm | 66 kB 00:00:00
(3/22): opendmarc-1.3.2-1.el7.x86_64.rpm | 94 kB 00:00:00
(4/22): perl-Business-ISBN-2.06-2.el7.noarch.rpm | 25 kB 00:00:00
(5/22): mailcap-2.1.41-2.el7.noarch.rpm | 31 kB 00:00:00
(6/22): perl-Compress-Raw-Bzip2-2.061-3.el7.x86_64.rpm | 32 kB 00:00:00
(7/22): perl-DBD-MySQL-4.023-6.el7.x86_64.rpm | 140 kB 00:00:00
(8/22): perl-Business-ISBN-Data-20120719.001-2.el7.noarch.rpm | 24 kB 00:00:00
(9/22): perl-Compress-Raw-Zlib-2.061-4.el7.x86_64.rpm | 57 kB 00:00:00
(10/22): perl-Data-Dumper-2.145-3.el7.x86_64.rpm | 47 kB 00:00:00
(11/22): perl-DBI-1.627-4.el7.x86_64.rpm | 802 kB 00:00:00
(12/22): perl-HTTP-Date-6.02-8.el7.noarch.rpm | 14 kB 00:00:00
(13/22): perl-HTTP-Message-6.06-6.el7.noarch.rpm | 82 kB 00:00:00
(14/22): perl-LWP-MediaTypes-6.02-2.el7.noarch.rpm | 24 kB 00:00:00
(15/22): perl-IO-Compress-2.061-2.el7.noarch.rpm | 260 kB 00:00:00
(16/22): perl-IO-HTML-1.00-2.el7.noarch.rpm | 23 kB 00:00:00
(17/22): perl-Encode-Locale-1.03-5.el7.noarch.rpm | 16 kB 00:00:00
(18/22): perl-PlRPC-0.2020-14.el7.noarch.rpm | 36 kB 00:00:00
(19/22): perl-Net-Daemon-0.48-5.el7.noarch.rpm | 51 kB 00:00:00
(20/22): perl-TimeDate-2.30-2.el7.noarch.rpm | 52 kB 00:00:00
(21/22): perl-URI-1.60-9.el7.noarch.rpm | 106 kB 00:00:00
(22/22): perl-Switch-2.16-7.el7.noarch.rpm | 22 kB 00:00:00
---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Total 1.9 MB/s | 2.0 MB 00:00:01
Running transaction check
Running transaction test
Transaction test succeeded
Running transaction
Installing : perl-Data-Dumper-2.145-3.el7.x86_64 1/22
Installing : libspf2-1.2.10-5.20150405gitd57d79fd.el7.x86_64 2/22
Installing : 1:perl-Compress-Raw-Zlib-2.061-4.el7.x86_64 3/22
Installing : libopendmarc-1.3.2-1.el7.x86_64 4/22
Installing : perl-Switch-2.16-7.el7.noarch 5/22
Installing : 1:perl-TimeDate-2.30-2.el7.noarch 6/22
Installing : perl-HTTP-Date-6.02-8.el7.noarch 7/22
Installing : perl-IO-HTML-1.00-2.el7.noarch 8/22
Installing : perl-Encode-Locale-1.03-5.el7.noarch 9/22
Installing : perl-Business-ISBN-Data-20120719.001-2.el7.noarch 10/22
Installing : perl-Business-ISBN-2.06-2.el7.noarch 11/22
Installing : perl-URI-1.60-9.el7.noarch 12/22
Installing : perl-Net-Daemon-0.48-5.el7.noarch 13/22
Installing : perl-Compress-Raw-Bzip2-2.061-3.el7.x86_64 14/22
Installing : perl-IO-Compress-2.061-2.el7.noarch 15/22
Installing : perl-PlRPC-0.2020-14.el7.noarch 16/22
Installing : perl-DBI-1.627-4.el7.x86_64 17/22
Installing : perl-DBD-MySQL-4.023-6.el7.x86_64 18/22
Installing : mailcap-2.1.41-2.el7.noarch 19/22
Installing : perl-LWP-MediaTypes-6.02-2.el7.noarch 20/22
Installing : perl-HTTP-Message-6.06-6.el7.noarch 21/22
Installing : opendmarc-1.3.2-1.el7.x86_64 22/22
Verifying : perl-Business-ISBN-2.06-2.el7.noarch 1/22
Verifying : mailcap-2.1.41-2.el7.noarch 2/22
Verifying : perl-IO-Compress-2.061-2.el7.noarch 3/22
Verifying : perl-Compress-Raw-Bzip2-2.061-3.el7.x86_64 4/22
Verifying : perl-Net-Daemon-0.48-5.el7.noarch 5/22
Verifying : perl-HTTP-Date-6.02-8.el7.noarch 6/22
Verifying : perl-HTTP-Message-6.06-6.el7.noarch 7/22
Verifying : perl-Business-ISBN-Data-20120719.001-2.el7.noarch 8/22
Verifying : perl-DBI-1.627-4.el7.x86_64 9/22
Verifying : perl-Encode-Locale-1.03-5.el7.noarch 10/22
Verifying : perl-Data-Dumper-2.145-3.el7.x86_64 11/22
Verifying : opendmarc-1.3.2-1.el7.x86_64 12/22
Verifying : 1:perl-Compress-Raw-Zlib-2.061-4.el7.x86_64 13/22
Verifying : perl-LWP-MediaTypes-6.02-2.el7.noarch 14/22
Verifying : perl-IO-HTML-1.00-2.el7.noarch 15/22
Verifying : perl-PlRPC-0.2020-14.el7.noarch 16/22
Verifying : libopendmarc-1.3.2-1.el7.x86_64 17/22
Verifying : 1:perl-TimeDate-2.30-2.el7.noarch 18/22
Verifying : perl-Switch-2.16-7.el7.noarch 19/22
Verifying : perl-DBD-MySQL-4.023-6.el7.x86_64 20/22
Verifying : perl-URI-1.60-9.el7.noarch 21/22
Verifying : libspf2-1.2.10-5.20150405gitd57d79fd.el7.x86_64 22/22
Installed:
opendmarc.x86_64 0:1.3.2-1.el7
Dependency Installed:
libopendmarc.x86_64 0:1.3.2-1.el7 libspf2.x86_64 0:1.2.10-5.20150405gitd57d79fd.el7 mailcap.noarch 0:2.1.41-2.el7 perl-Business-ISBN.noarch 0:2.06-2.el7 perl-Business-ISBN-Data.noarch 0:20120719.001-2.el7
perl-Compress-Raw-Bzip2.x86_64 0:2.061-3.el7 perl-Compress-Raw-Zlib.x86_64 1:2.061-4.el7 perl-DBD-MySQL.x86_64 0:4.023-6.el7 perl-DBI.x86_64 0:1.627-4.el7 perl-Data-Dumper.x86_64 0:2.145-3.el7
perl-Encode-Locale.noarch 0:1.03-5.el7 perl-HTTP-Date.noarch 0:6.02-8.el7 perl-HTTP-Message.noarch 0:6.06-6.el7 perl-IO-Compress.noarch 0:2.061-2.el7 perl-IO-HTML.noarch 0:1.00-2.el7
perl-LWP-MediaTypes.noarch 0:6.02-2.el7 perl-Net-Daemon.noarch 0:0.48-5.el7 perl-PlRPC.noarch 0:0.2020-14.el7 perl-Switch.noarch 0:2.16-7.el7 perl-TimeDate.noarch 1:2.30-2.el7
perl-URI.noarch 0:1.60-9.el7
Complete!
Step 2: Configuration
Here's the default configuration (from /etc/dmarc.conf):
##
## Copyright (c) 2012-2015, The Trusted Domain Project. All rights reserved.
## DEPRECATED CONFIGURATION OPTIONS
##
## The following configuration options are no longer valid. They should be
## removed from your existing configuration file to prevent potential issues.
## Failure to do so may result in opendmarc being unable to start.
##
## Renamed in 1.3.0:
## ForensicReports became FailureReports
## ForensicReportsBcc became FailureReportsBcc
## ForensicReportsOnNone became FailureReportsOnNone
## ForensicReportsSentBy became FailureReportsSentBy
## CONFIGURATION OPTIONS
## AuthservID (string)
## defaults to MTA name
##
## Sets the "authserv-id" to use when generating the Authentication-Results:
## header field after verifying a message. If the string "HOSTNAME" is
## provided, the name of the host running the filter (as returned by the
## gethostname(3) function) will be used.
#
# AuthservID name
## AuthservIDWithJobID { true | false }
## default "false"
##
## If "true", requests that the authserv-id portion of the added
## Authentication-Results header fields contain the job ID of the message
## being evaluated.
#
# AuthservIDWithJobID false
## AutoRestart { true | false }
## default "false"
##
## Automatically re-start on failures. Use with caution; if the filter fails
## instantly after it starts, this can cause a tight fork(2) loop.
#
# AutoRestart false
## AutoRestartCount n
## default 0
##
## Sets the maximum automatic restart count. After this number of automatic
## restarts, the filter will give up and terminate. A value of 0 implies no
## limit.
#
# AutoRestartCount 0
## AutoRestartRate n/t[u]
## default (no limit)
##
## Sets the maximum automatic restart rate. If the filter begins restarting
## faster than the rate defined here, it will give up and terminate. This
## is a string of the form n/t[u] where n is an integer limiting the count
## of restarts in the given interval and t[u] defines the time interval
## through which the rate is calculated; t is an integer and u defines the
## units thus represented ("s" or "S" for seconds, the default; "m" or "M"
## for minutes; "h" or "H" for hours; "d" or "D" for days). For example, a
## value of "10/1h" limits the restarts to 10 in one hour. There is no
## default, meaning restart rate is not limited.
#
# AutoRestartRate n/t[u]
## Background { true | false }
## default "true"
##
## Causes opendmarc to fork and exits immediately, leaving the service
## running in the background.
#
# Background true
## BaseDirectory (string)
## default (none)
##
## If set, instructs the filter to change to the specified directory using
## chdir(2) before doing anything else. This means any files referenced
## elsewhere in the configuration file can be specified relative to this
## directory. It's also useful for arranging that any crash dumps will be
## saved to a specific location.
#
# BaseDirectory /var/run/opendmarc
## ChangeRootDirectory (string)
## default (none)
##
## Requests that the operating system change the effective root directory of
## the process to the one specified here prior to beginning execution.
## chroot(2) requires superuser access. A warning will be generated if
## UserID is not also set.
#
# ChangeRootDirectory /var/chroot/opendmarc
## CopyFailuresTo (string)
## default (none)
##
## Requests addition of the specified email address to the envelope of
## any message that fails the DMARC evaluation.
#
# CopyFailuresTo postmaster@localhost
## DNSTimeout (integer)
## default 5
##
## Sets the DNS timeout in seconds. A value of 0 causes an infinite wait.
## (NOT YET IMPLEMENTED)
#
# DNSTimeout 5
## EnableCoredumps { true | false }
## default "false"
##
## On systems that have such support, make an explicit request to the kernel
## to dump cores when the filter crashes for some reason. Some modern UNIX
## systems suppress core dumps during crashes for security reasons if the
## user ID has changed during the lifetime of the process. Currently only
## supported on Linux.
#
# EnableCoreDumps false
## FailureReports { true | false }
## default "false"
##
## Enables generation of failure reports when the DMARC test fails and the
## purported sender of the message has requested such reports. Reports are
## formatted per RFC6591.
#
# FailureReports false
## FailureReportsBcc (string)
## default (none)
##
## When failure reports are enabled and one is to be generated, always
## send one to the address(es) specified here. If a failure report is
## requested by the domain owner, the address(es) are added in a Bcc: field.
## If no request is made, they address(es) are used in a To: field. There
## is no default.
#
# FailureReportsBcc postmaster@example.coom
## FailureReportsOnNone { true | false }
## default "false"
##
## Supplements the "FailureReports" setting by generating reports for
## domains that advertise "none" policies. By default, reports are only
## generated (when enabled) for sending domains advertising a "quarantine"
## or "reject" policy.
#
# FailureReportsOnNone false
## FailureReportsSentBy string
## default "USER@HOSTNAME"
##
## Specifies the email address to use in the From: field of failure
## reports generated by the filter. The default is to use the userid of
## the user running the filter and the local hostname to construct an
## email address. "postmaster" is used in place of the userid if a name
## could not be determined.
#
# FailureReportsSentBy USER@HOSTNAME
## HistoryFile path
## default (none)
##
## If set, specifies the location of a text file to which records are written
## that can be used to generate DMARC aggregate reports. Records are groups
## of rows containing information about a single received message, and
## include all relevant information needed to generate a DMARC aggregate
## report. It is expected that this will not be used in its raw form, but
## rather periodically imported into a relational database from which the
## aggregate reports can be extracted by a tool such as opendmarc-import(8).
#
# HistoryFile /var/spool/opendmarc/opendmarc.dat
## IgnoreAuthenticatedClients { true | false }
## default "false"
##
## If set, causes mail from authenticated clients (i.e., those that used
## SMTP AUTH) to be ignored by the filter.
#
# IgnoreAuthenticatedClients false
## IgnoreHosts path
## default (internal)
##
## Specifies the path to a file that contains a list of hostnames, IP
## addresses, and/or CIDR expressions identifying hosts whose SMTP
## connections are to be ignored by the filter. If not specified, defaults
## to "127.0.0.1" only.
#
# IgnoreHosts /etc/opendmarc/ignore.hosts
## IgnoreMailFrom domain[,...]
## default (none)
##
## Gives a list of domain names whose mail (based on the From: domain) is to
## be ignored by the filter. The list should be comma-separated. Matching
## against this list is case-insensitive. The default is an empty list,
## meaning no mail is ignored.
#
# IgnoreMailFrom example.com
## MilterDebug (integer)
## default 0
##
## Sets the debug level to be requested from the milter library.
#
# MilterDebug 0
## PidFile path
## default (none)
##
## Specifies the path to a file that should be created at process start
## containing the process ID.
#
# PidFile /var/run/opendmarc.pid
## PublicSuffixList path
## default (none)
##
## Specifies the path to a file that contains top-level domains (TLDs) that
## will be used to compute the Organizational Domain for a given domain name,
## as described in the DMARC specification. If not provided, the filter will
## not be able to determine the Organizational Domain and only the presented
## domain will be evaluated.
#
# PublicSuffixList path
## RecordAllMessages { true | false }
## default "false"
##
## If set and "HistoryFile" is in use, all received messages are recorded
## to the history file. If not set (the default), only messages for which
## the From: domain published a DMARC record will be recorded in the
## history file.
#
# RecordAllMessages false
## RejectFailures { true | false }
## default "false"
##
## If set, messages will be rejected if they fail the DMARC evaluation, or
## temp-failed if evaluation could not be completed. By default, no message
## will be rejected or temp-failed regardless of the outcome of the DMARC
## evaluation of the message. Instead, an Authentication-Results header
## field will be added.
#
# RejectFailures false
## ReportCommand string
## default "/usr/sbin/sendmail -t"
##
## Indicates the shell command to which failure reports should be passed for
## delivery when "FailureReports" is enabled.
#
# ReportCommand /usr/sbin/sendmail -t
## RequiredHeaders { true | false }
## default "false"
##
## If set, the filter will ensure the header of the message conforms to the
## basic header field count restrictions laid out in RFC5322, Section 3.6.
## Messages failing this test are rejected without further processing. A
## From: field from which no domain name could be extracted will also be
## rejected.
#
# RequiredHeaders false
## Socket socketspec
## default (none)
##
## Specifies the socket that should be established by the filter to receive
## connections from sendmail(8) in order to provide service. socketspec is
## in one of two forms: local:path, which creates a UNIX domain socket at
## the specified path, or inet:port[@host] or inet6:port[@host] which creates
## a TCP socket on the specified port for the appropriate protocol family.
## If the host is not given as either a hostname or an IP address, the
## socket will be listening on all interfaces. This option is mandatory
## either in the configuration file or on the command line. If an IP
## address is used, it must be enclosed in square brackets.
#
Socket inet:8893@localhost
## SoftwareHeader { true | false }
## default "false"
##
## Causes the filter to add a "DMARC-Filter" header field indicating the
## presence of this filter in the path of the message from injection to
## delivery. The product's name, version, and the job ID are included in
## the header field's contents.
#
SoftwareHeader true
## SPFIgnoreResults { true | false }
## default "false"
##
## Causes the filter to ignore any SPF results in the header of the
## message. This is useful if you want the filter to perfrom SPF checks
## itself, or because you don't trust the arriving header.
#
SPFIgnoreResults true
## SPFSelfValidate { true | false }
## default false
##
## Enable internal spf checking with --with-spf
## To use libspf2 instead: --with-spf --with-spf2-include=path --with-spf2-lib=path
##
## Causes the filter to perform a fallback SPF check itself when
## it can find no SPF results in the message header. If SPFIgnoreResults
## is also set, it never looks for SPF results in headers and
## always performs the SPF check itself when this is set.
#
SPFSelfValidate true
## Syslog { true | false }
## default "false"
##
## Log via calls to syslog(3) any interesting activity.
#
Syslog true
## SyslogFacility facility-name
## default "mail"
##
## Log via calls to syslog(3) using the named facility. The facility names
## are the same as the ones allowed in syslog.conf(5).
#
# SyslogFacility mail
## TrustedAuthservIDs string
## default HOSTNAME
##
## Specifies one or more "authserv-id" values to trust as relaying true
## upstream DKIM and SPF results. The default is to use the name of
## the MTA processing the message. To specify a list, separate each entry
## with a comma. The key word "HOSTNAME" will be replaced by the name of
## the host running the filter as reported by the gethostname(3) function.
#
# TrustedAuthservIDs HOSTNAME
## UMask mask
## default (none)
##
## Requests a specific permissions mask to be used for file creation. This
## only really applies to creation of the socket when Socket specifies a
## UNIX domain socket, and to the HistoryFile and PidFile (if any); temporary
## files are normally created by the mkstemp(3) function that enforces a
## specific file mode on creation regardless of the process umask. See
## umask(2) for more information.
#
UMask 007
## UserID user[:group]
## default (none)
##
## Attempts to become the specified userid before starting operations.
## The process will be assigned all of the groups and primary group ID of
## the named userid unless an alternate group is specified.
#
UserID opendmarc:mail
AuthservID (string)
Sets the "authserv-id" to use when generating the Authentication-Results: header field after verifying a message.
The default is to use the name of the MTA processing the message. If the string "HOSTNAME" is provided, the name of the host running the filter (as returned by the gethostname(3) function) will be used.
Set IgnoreAuthenticatedClients true, otherwise authenticated messages will fail DMARC.
Step 3: Perform Service Setup
Created symlink from /etc/systemd/system/multi-user.target.wants/opendmarc.service to /usr/lib/systemd/system/opendmarc.service.
# systemctl start opendmarc
# systemctl status opendmarc
● opendmarc.service - Domain-based Message Authentication, Reporting & Conformance (DMARC) Milter
Loaded: loaded (/usr/lib/systemd/system/opendmarc.service; enabled; vendor preset: disabled)
Active: active (running) since Thu 2020-07-30 16:12:56 EEST; 5s ago
Docs: man:opendmarc(8)
man:opendmarc.conf(5)
man:opendmarc-import(8)
man:opendmarc-reports(8)
http://www.trusteddomain.org/opendmarc/
Process: 22011 ExecStart=/usr/sbin/opendmarc $OPTIONS (code=exited, status=0/SUCCESS)
Main PID: 22012 (opendmarc)
CGroup: /system.slice/opendmarc.service
└─22012 /usr/sbin/opendmarc -c /etc/opendmarc.conf -P /var/run/opendmarc/opendmarc.pid
Jul 30 16:12:56 mail.domain.tld systemd[1]: Starting Domain-based Message Authentication, Reporting & Conformance (DMARC) Milter...
Jul 30 16:12:56 mail.domain.tld opendmarc[22012]: OpenDMARC Filter v1.3.2 starting (args: -c /etc/opendmarc.conf -P /var/run/opendmarc/opendmarc.pid)
Jul 30 16:12:56 mail.domain.tld opendmarc[22012]: additional trusted authentication services: mail.domain.tld
Jul 30 16:12:56 mail.domain.tld systemd[1]: Started Domain-based Message Authentication, Reporting & Conformance (DMARC) Milter.
Step 4: Integrate with Axigen
From WebAdmin: create an advance routing rule for defining the DMARC Milter filter using the onConnect event.
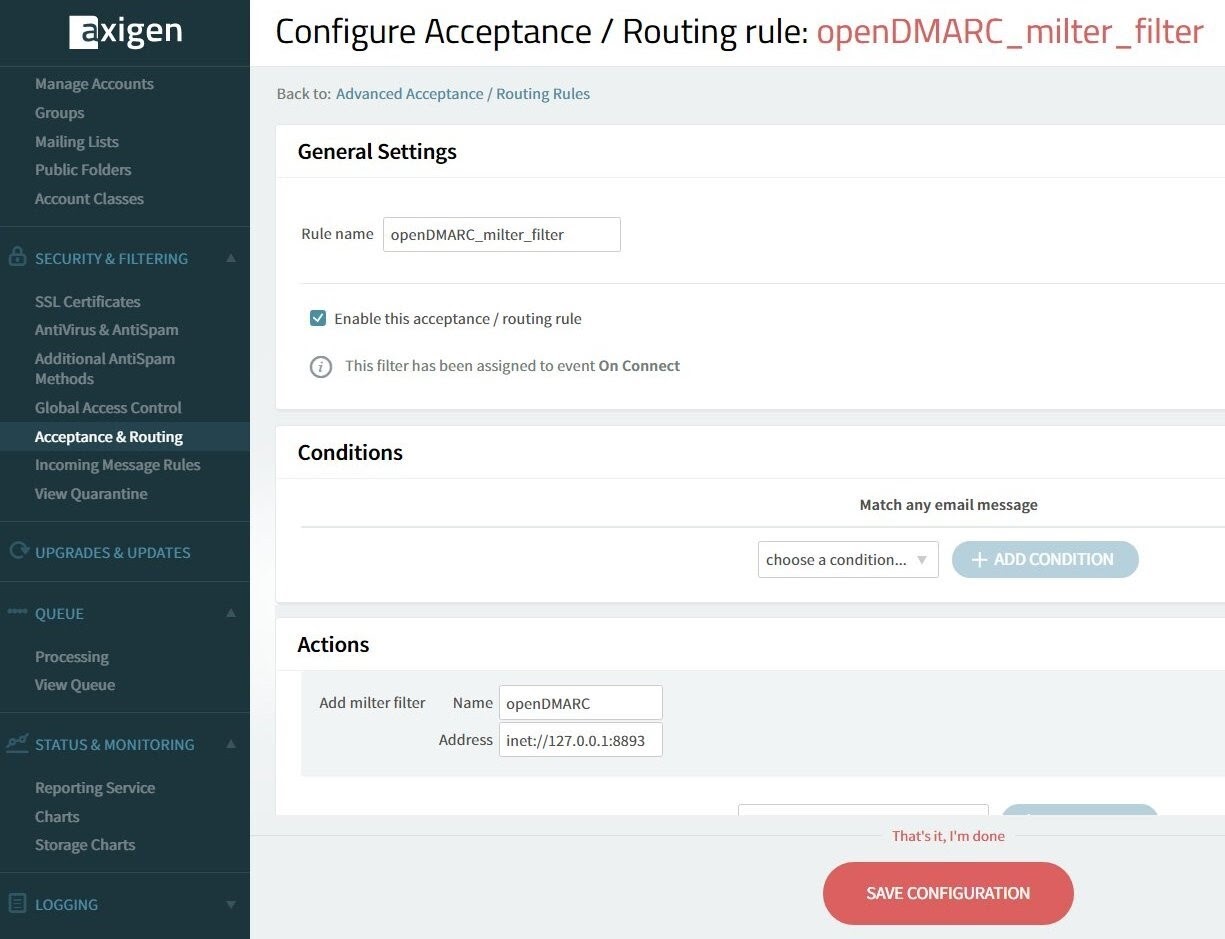
set (filterName, "openDMARC");
set (filterType, "milter");
set (filterAddress, "inet://127.0.0.1:8893");
call (addFilter);
}
Then create an advanced routing rule for executing the DMARC milter filter on every event.
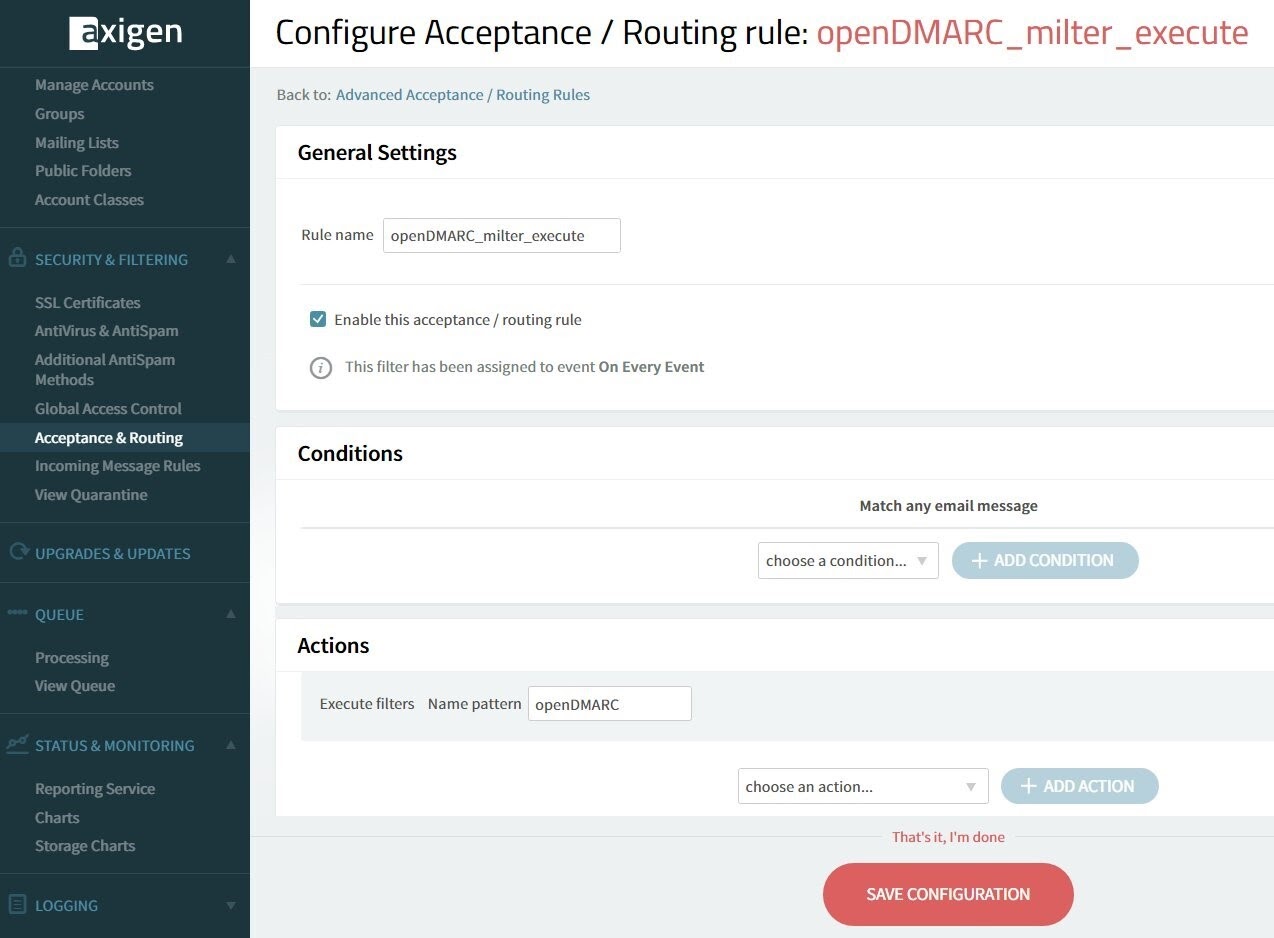
set (filterNamePattern, "openDMARC");
call (executeFilters);
}
Step 5: Logging
Jul 30 16:12:56 mail opendmarc[22012]: OpenDMARC Filter v1.3.2 starting (args: -c /etc/opendmarc.conf -P /var/run/opendmarc/opendmarc.pid)
Jul 30 16:12:56 mail opendmarc[22012]: additional trusted authentication services: mail.domain.tld
Jul 30 16:17:37 mail opendmarc[22012]: 2881554: SPF(mailfrom): test@yahoo.com pass
Jul 30 16:17:37 mail opendmarc[22012]: 2881554: yahoo.com pass
Jul 30 16:47:39 mail opendmarc[22012]: 3340019: SPF(mailfrom): example@test.family pass
Jul 30 16:47:39 mail opendmarc[22012]: 3340019: moldovan.family none
Jul 30 16:57:52 mail opendmarc[22012]: 1536933: SPF(mailfrom): example@test.family pass
Jul 30 16:57:52 mail opendmarc[22012]: 1536933: test.family pass
Jul 30 23:17:13 mail opendmarc[22012]: 1232461: SPF(mailfrom): test@yahoo.com fail
Jul 30 23:17:13 mail opendmarc[22012]: 1232461: yahoo.com fail
Jul 30 23:27:21 mail opendmarc[23417]: 3371752: SPF(mailfrom): test@yahoo.com tempfail
Jul 30 23:27:45 mail opendmarc[23417]: 3371752: yahoo.com none
Step 6: Test and Check Results
Header examples:
From Gmail:
209.85.210.41 as permitted sender) client-ip=209.85.210.41;
envelope-from=test@gmail.com; mechanism=include; identity=mailfrom;
receiver=mail.domain.tld;
X-AXIGEN-SPF-Result: Ok
Authentication-Results: mail.domain.tld;
spf=pass smtp.mailfrom=test@gmail.com
Authentication-Results: mail.domain.tld; dmarc=pass (p=none dis=none)
header.from=gmail.com
DMARC-Filter: OpenDMARC Filter v1.3.2 1549720
From Yahoo:
98.137.68.147 as permitted sender) client-ip=98.137.68.147;
envelope-from=test@yahoo.com; mechanism=ptr; identity=mailfrom;
receiver=mail.domain.tld;
X-AXIGEN-SPF-Result: Ok
Authentication-Results: mail.domain.tld;
spf=pass smtp.mailfrom=test@yahoo.com
Authentication-Results: mail.domain.tld; dmarc=pass (p=reject dis=none)
header.from=yahoo.com
DMARC-Filter: OpenDMARC Filter v1.3.2 1502717
Pretending to send from Yahoo (email impersonation):
by domain of test@yahoo.com) client-ip=78.97.91.153;
envelope-from=test@yahoo.com; mechanism=default; identity=mailfrom;
receiver=mail.domain.tld;
X-AXIGEN-SPF-Result: Uncertain
Authentication-Results: mail.domain.tld;
spf=fail smtp.mailfrom=test@yahoo.com
Authentication-Results: mail.domain.tld; dmarc=fail (p=reject dis=none)
header.from=yahoo.com
DMARC-Filter: OpenDMARC Filter v1.3.2 1232461
How to Filter Messages Based on the DMARC Policy
Using the Axigen X3 Update 2 openDMARC integration, you can choose what you want to happen to messages, based on the DMARC policy they’ve been attributed to. You can choose to either reject or quarantine them, or to accept them, but file them in the Spam folder.
Reject / Quarantine Failures
- /etc/opendmarc.conf is set to RejectFailures true
- message reject when DMARC policy p=reject
- message quarantine when DMARC policy p=quarantine
SMTP-IN:00000004: [MILTER] Filter responded with 'a' (accept message)
Message has been accepted !!!
- message temp-fail when DMARC check could not be performed
SMTP-IN:0000003D: [MILTER] Filter responded with 'a' (accept message)
Message has been accepted !!!
Accept Failures but File them in Spam
- /etc/opendmarc.conf is set to RejectFailures false
- Axigen server side Sieve filter in filters/wasieve-server.sieve
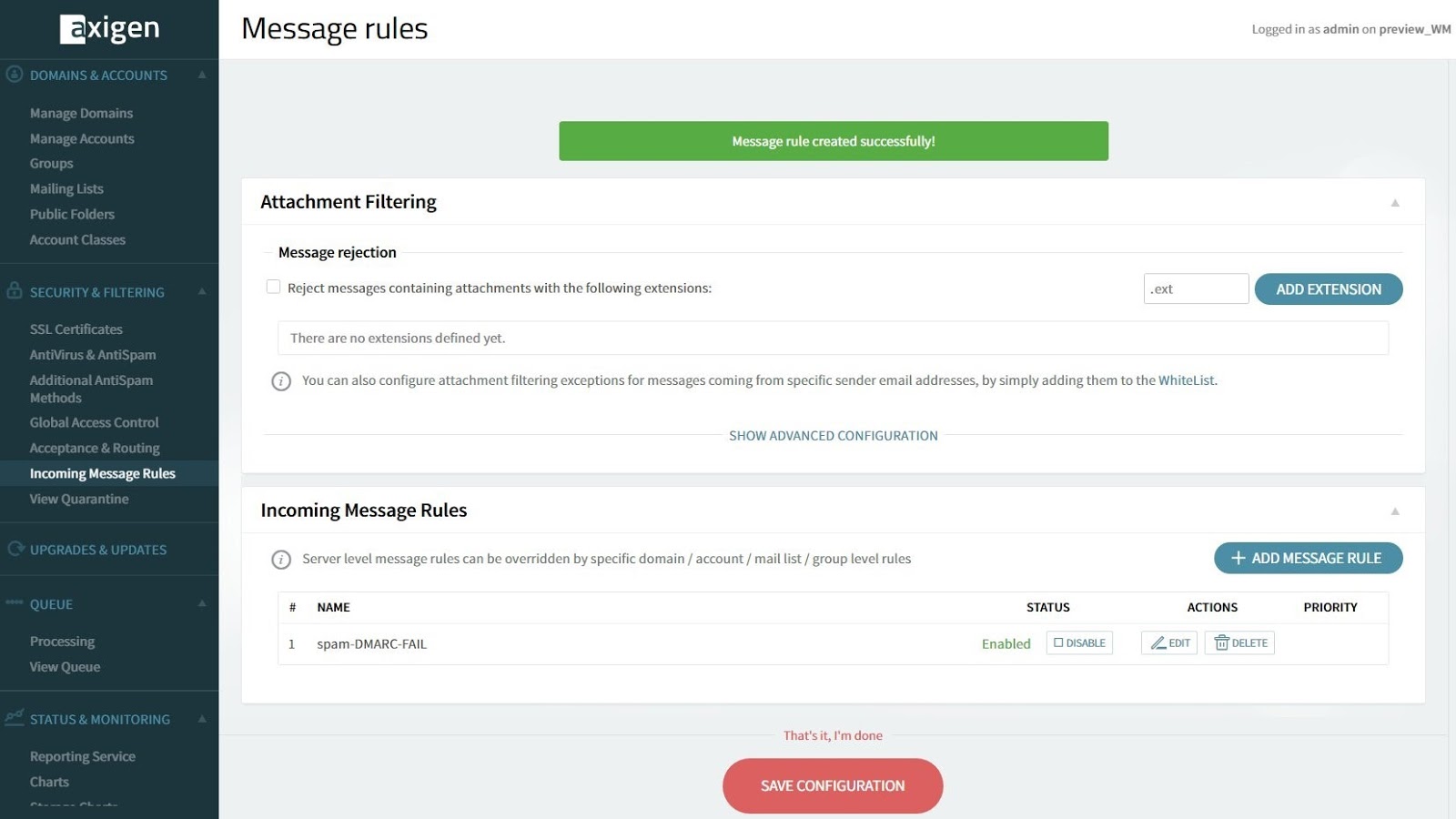
if anyof (
header :contains ["Authentication-Results"] ["; dmarc=fail ("]
) {
fileinto "Spam";
stop;
}
PROCESSING:0011969C: Fileinto [Spam] requested for <test@domain.tld>
Summing Up
We hope this guide to integrating Axigen X3 with openDMARC via Milter V6 was useful & that you managed to complete all the steps. If not, feel free to reach out to us.
For more info on Axigen architecture, installation, and administration, visit our documentation section.